When looking for a security advisor, people ask the wrong questions

Independent Security Risk Advisor – I cannot understand how these questions will help them find the best Security Advisor or Security Risk Assessor.
They might be asking the wrong questions because they are unfamiliar with the industry. They could potentially be approaching the matter like they would approach finding the Best Security Company. This is not the right way to go about it. There are vast differences between a security risk assessor or advisor and a security company.
On this page, we will address and discuss the correct types of questions to ask when you are looking for the right Independence Security Risk Assessor.
We recently conducted an independent security risk assessment for a manufacturing plant in Cape Town, identifying risks often overlooked by standard assessments. Our independent approach enabled us to recommend practical measures to improve the safety of employees, assets, and the facility.
If you would like to learn more about our assessments or have specific topics you would like us to address, please email your suggestions to andre@alwinco.co.za. We will create and publish articles tailored to your interests on our website.
Question 1: The Law
One of the first things you need to know is that any person who works with any security-related products or services must be registered at PSIRA. This means that the person who is doing the work, whether installing, servicing, guarding, selling, or advising, AS WELL AS the company that this person is employed at, must be registered at PSIRA. When you employ someone to install security hardware at your premises, they need to provide you with two PSIRA certificates: one for the company and one for the employee who is doing the installation. The security law pertinently states that if you use an unregistered security person, you make yourself guilty and could be fined. The security law further states that it is expected of a person to ensure that the security persons are registered at PSIRA before they take them into their employ.
Question 2: Vetting
Vetting is another essential aspect that must be considered when searching for a Security Risk Assessor. One way to vet an assessor is to see how many articles they have published online and in magazines. Remember, as an Assessor, I can tell you anything you want to hear, but I have to be able to back it up with something credible. Some people can sell themselves, but they do not have the experience or knowledge to do the job. Articles regarding security that the Assessor has written and published in various independent sources indicate what this person is capable of.
Question 3: Sharing information
Keep in mind that if you write an article and publish it for everyone to see, you will get a lot of questions, criticism, possibly some backlash, and so on. An Assessor will not publish an article if they cannot back it up. When the ‘sales pitch is the same as the articles, you know that this person can do what he says and is legitimate. People will know him, and if the information in the articles does not match the information about the assessor, they will call him out. In addition to this, a Security Risk Assessor needs to have crime scene experience. I am talking about real-life crime scenes, not those explained in a handbook or on television. Experience in interviewing criminals, suspects, and victims alike is essential, as this gives you another viewpoint regarding crime. Understanding risk is a vital aspect of being a Security Risk Assessor.
Question 4: The solution
An essential aspect to remember is that a security risk assessor or advisor is never part of the solution. Nor will they sell or install any security hardware, software, or services. When a Security Risk Assessor sells hardware, software, or services such as guarding, he cannot be unbiased. He will focus on selling his products rather than finding the risks and getting suitable solutions.
Question 5: Google Search
Another approach to researching the assessor or advisor is to type their name into Google and see what pops up. Example: André Mundell. You can also search the company name for information. Example (Alwinco). This will indicate how active and up-to-date this person and company are in the security world. A Security Risk Assessor or Advisor cannot be part of or affiliated with any security company. This individual needs to be independent. The security risk assessor’s or advisor’s income should solely be derived from their assessments. The assessor or advisor cannot receive any kickbacks from a security company or a hardware supplier.
Question 6: Understand the difference
It is also vital that the assessor or advisor understand the difference between a security risk assessment and risk management, as well as the difference between a security risk assessment and health & safety.
Question 7: Public Speaking
Another indication of a good Security Risk Assessor is to find out if they are involved in public speaking events relating to security. Suppose this person has enough knowledge, information, and the necessary backup to prove what he is saying. In that case, you know that he is credible, reliable, and able to do the work. The security risk assessor or advisor should provide a clearance certificate that confirms they are not involved in any crime-related activities.They should update this certificate annually.Having these documents (PSIRA and the Clearance Certificate) gives you an advantage, as you have more than just a person’s name and company name. Now you have their fingerprints as well. The clearance certificate number will give you access to the fingerprints when needed.
A Security Risk Assessor also needs to understand that the functionality of a Security Matrix cannot be used to measure Risk. Opportunity measures risk, not from high to low.
Question 8: Confidentiality
Confidentiality is another essential aspect that the risk assessor or advisor should respect. Confidentiality does not have a sell-by date. When a risk assessor or advisor gives you a list of all his previous and current clients, you should reconsider because that is a breach of confidentiality. Providing a list of names is, in essence, a huge security risk. Our article, ‘Loose lips sink the ship’, has references. I believe that the POPI Act that will take effect might prevent assessors and advisors from disclosing their clients’ names. In addition to this, the risk assessor or advisor should understand public violence, as this has become part of South African culture.
Question 9: Security Provider
We have previously said this in one of our articles, but it is essential, and I would like to share it again. To get someone from your current Security Provider to conduct a Security Risk Assessment on your property is like asking your mother if you are fat. She will tell you that you are beautiful or handsome and that you have never looked better because she loves you, and she does not want to hurt your feelings, even if you look like an elephant. A little white lie from your mom about your appearance will not shatter your life into pieces. However, a ‘little white lie’ from an in-house assessor might just rip several lives if crime strikes.
Question 10: In-house assessor
An in-house assessor is the same. They will not want to step on toes or make their managers and the security company unhappy. So, they will say what they need to say to keep everyone happy. Keeping everyone happy will not eliminate the risks. A good Security Risk Assessor knows that it is sometimes worth stepping on toes if this means that the security risks will be identified.
I genuinely hope that this guide will give you the information you need to make the right decision regarding an independent Security Risk Assessor.
Question 11: understand the Viewpoints
A Security Risk Assessor needs to understand all five different viewpoints. He also needs to know how to use them to his advantage regarding crime and security.
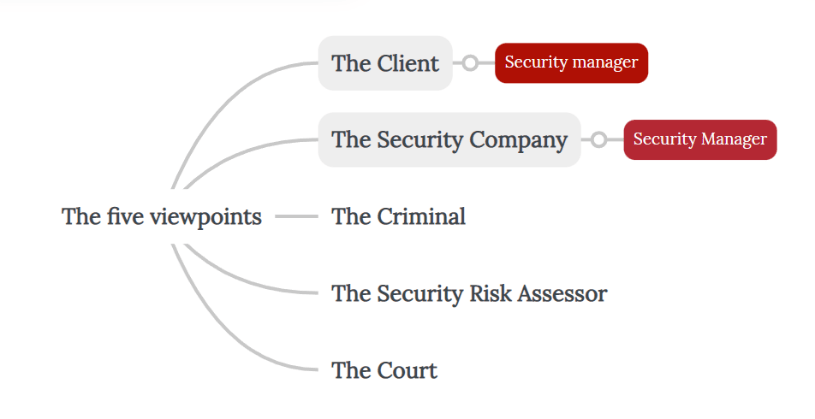 The Client
The Client
- Security Manager
- The Security Company
- Security Manager
- The Criminal
- The Security Risk Assessor
- The Court
Read more on independent security risk consultants.
Written by André Mundell, Independent Risk Assessor. # Independent Security Risk Advisor
We conduct security risk assessments for customers in Moreleta Park, Bloemfontein, Berea, Glen Austin, Cape Town, and other locations in Gauteng. These assessments include homes, businesses, industrial estates, farms, and other types of properties.